I always find that I get this message when I ssh into a new machine:12:f8:7e:78:61:b4:bf:e2:de:24:15:96:4e:d4:72:53What does it stand for? Will every machine have the same fingerprint every ti. SSH key pairs allow an additional level of security that can be used in conjunction with the SFTP protocol. Key pairs are typically created by the client, and then the resulting public key is used by Core FTP Server. Core FTP products use the OpenSSH SSH2 format, that can be generated using Core FTP software, or via the ssh-keygen utility. SSH KeyGen is a simple process that creates a public/private SSH Key-pair that can be used to securely access a virtual private server. Get started on Windows via PuTTY Download or jump right in on. To connect to SSH without entering a password, you can generate public and private keys on the local north, then copy it to a remote machine, then the password will not be asked when connecting to.
-->Azure DevOps Services | Azure DevOps Server 2020 | Azure DevOps Server 2019 | TFS 2018 - TFS 2015
Connect to your Git repos through SSH on macOS, Linux, or Windows to securely connect using HTTPS authentication. On Windows, we recommended the use of Git Credential Manager Core or Personal Access Tokens.
Important
SSH URLs have changed, but old SSH URLs will continue to work. If you have already set up SSH, you should update your remote URLs to the new format:
- Verify which remotes are using SSH by running
git remote -vin your Git client. - Visit your repository on the web and select the Clone button in the upper right.
- Select SSH and copy the new SSH URL.
- In your Git client, run:
git remote set-url <remote name, e.g. origin> <new SSH URL>. Alternatively, in Visual Studio, go to Repository Settings, and edit your remotes.
Note
As of Visual Studio 2017, SSH can be used to connect to Azure DevOps Git repos.
How SSH key authentication works
SSH public key authentication works with an asymmetric pair of generated encryption keys. The public key is shared with Azure DevOps and used to verify the initial ssh connection. The private key is kept safe and secure on your system.
Set up SSH key authentication
The following steps cover configuration of SSH key authentication on the following platforms:
- Linux
- macOS running at least Leopard (10.5)
- Windows systems running Git for Windows
Configure SSH using the command line. bash is the common shell on Linux and macOS and the Git for Windows installation adds a shortcut to Git Bash in the Start menu.Other shell environments will work, but are not covered in this article.
Step 1: Create your SSH keys
Note
If you have already created SSH keys on your system, skip this step and go to configuring SSH keys.
The commands here will let you create new default SSH keys, overwriting existing default keys. Before continuing, check your~/.ssh folder (for example, /home/jamal/.ssh or C:Usersjamal.ssh) and look for the following files:
- id_rsa
- id_rsa.pub
If these files exist, then you have already created SSH keys. You can overwrite the keys with the following commands, or skip this step and go to configuring SSH keys to reuse these keys.
Create your SSH keys with the ssh-keygen command from the bash prompt. This command will create a 3072-bit RSA key for use with SSH. You can give a passphrasefor your private key when prompted—this passphrase provides another layer of security for your private key.If you give a passphrase, be sure to configure the SSH agent to cache your passphrase so you don't have to enter it every time you connect.
This command produces the two keys needed for SSH authentication: your private key ( id_rsa ) and the public key ( id_rsa.pub ). It is important to never share the contents of your private key. If the private key iscompromised, attackers can use it to trick servers into thinking the connection is coming from you.
Step 2: Add the public key to Azure DevOps Services/TFS
Associate the public key generated in the previous step with your user ID.
Open your security settings by browsing to the web portal and selecting your avatar in the upper right of theuser interface. Select SSH public keys in the menu that appears.
Select + New Key.
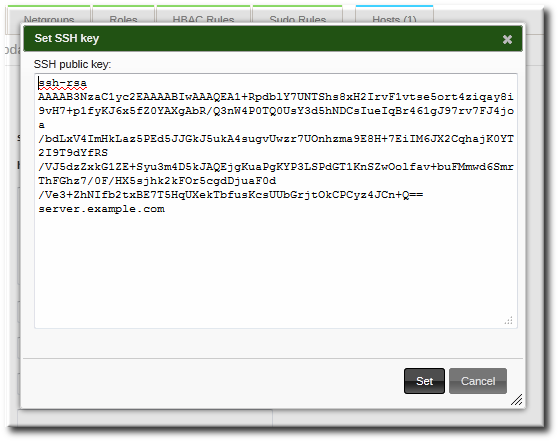
Copy the contents of the public key (for example, id_rsa.pub) that you generated into the Public Key Data field.
Important
Avoid adding whitespace or new lines into the Key Data field, as they can cause Azure DevOps Services to use an invalid public key. When pasting in the key, a newline often is added at the end. Be sure to remove this newline if it occurs.
Give the key a useful description (this description will be displayed on the SSH public keys page for your profile) so that you can remember it later. Select Save to store the public key.Once saved, you cannot change the key. You can delete the key or create a new entry for another key. There are no restrictions on how many keys you can add to your user profile. Also note that SSH keys stored in Azure DevOps expire after five years. If your key expires, you may upload a new key or the same one to continue accessing Azure DevOps via SSH.
Test the connection by running the following command:
ssh -T git@ssh.dev.azure.com.If everything is working correctly, you'll receive a response which says:remote: Shell access is not supported.If not, see the section on Questions and troubleshooting.
Step 2: Add the public key to Azure DevOps
Associate the public key generated in the previous step with your user ID.
Open your security settings by browsing to the web portal and selecting your avatar in the upper right of theuser interface. Select Security in the menu that appears.
Select + New Key.
Copy the contents of the public key (for example, id_rsa.pub) that you generated into the Public Key Data field.
Important
Avoid adding whitespace or new lines into the Key Data field, as they can cause Azure DevOps Services to use an invalid public key. When pasting in the key, a newline often is added at the end. Be sure to remove this newline if it occurs.
Give the key a useful description (this description will be displayed on the SSH public keys page for your profile) so that you can remember it later. Select Save to store the public key. Once saved, you cannot change the key. You can delete the key or create a new entry for another key. There are no restrictions on how many keys you can add to your user profile.
Test the connection by running the following command:
ssh -T git@ssh.dev.azure.com.If everything is working correctly, you'll receive a response which says:remote: Shell access is not supported.If not, see the section on Questions and troubleshooting.
Step 3: Clone the Git repository with SSH
Note
To connect with SSH from an existing cloned repo, see updating your remotes to SSH.
Copy the SSH clone URL from the web portal. In this example, the SSL clone URL is for a repo in an organization named fabrikam-fiber, as indicated by the first part of the URL after
dev.azure.com.Note
Project URLs have changed with the release of Azure DevOps Services and now have the format
dev.azure.com/{your organization}/{your project}, but you can still use the existingvisualstudio.comformat. For more information, see Visual Studio Team Services is now Azure DevOps Services.Run
git clonefrom the command prompt.
SSH may display the server's SSH fingerprint and ask you to verify it.You should verify that the displayed fingerprint matches one of the fingerprints in the SSH public keys page.
SSH displays this fingerprint when it connects to an unknown host to protect you from man-in-the-middle attacks.Once you accept the host's fingerprint, SSH will not prompt you again unless the fingerprint changes.
When you are asked if you want to continue connecting, type yes. Git will clone the repo and set up the origin remote to connect with SSH for future Git commands.
Tip
To prevent problems, Windows users should run a command to have Git reuse their SSH key passphrase.
Questions and troubleshooting
Q: After running git clone, I get the following error. What should I do?
A: Manually record the SSH key by running:ssh-keyscan -t rsa domain.com >> ~/.ssh/known_hosts
Q: How can I have Git remember the passphrase for my key on Windows?
A: Run the following command included in Git for Windows to start up the ssh-agent process in PowerShell or the Windows Command Prompt. ssh-agent will cacheyour passphrase so you don't have to provide it every time you connect to your repo.
If you're using the Bash shell (including Git Bash), start ssh-agent with:
Q: I use PuTTY as my SSH client and generated my keys with PuTTYgen. Can I use these keys with Azure DevOps Services?
A: Yes. Load the private key with PuTTYgen, go to Conversions menu and select Export OpenSSH key.Save the private key file and then follow the steps to set up non-default keys.Copy your public key directly from the PuTTYgen window and paste into the Key Data field in your security settings.
Q: How can I verify that the public key I uploaded is the same key as I have locally?
A: You can verify the fingerprint of the public key uploaded with the one displayed in your profile through the following ssh-keygen command run against your public key usingthe bash command line. You will need to change the path and the public key filename if you are not using the defaults.
You can then compare the MD5 signature to the one in your profile. This check is useful if you have connection problems or have concerns about incorrectlypasting in the public key into the Key Data field when adding the key to Azure DevOps Services.
Q: How can I start using SSH in a repository where I am currently using HTTPS?
A: You'll need to update the origin remote in Git to change over from a HTTPS to SSH URL. Once you have the SSH clone URL, run the following command:
You can now run any Git command that connects to origin.
Q: I'm using Git LFS with Azure DevOps Services and I get errors when pulling files tracked by Git LFS.
A: Azure DevOps Services currently doesn't support LFS over SSH. Use HTTPS to connect to repos with Git LFS tracked files.
Q: How can I use a non-default key location, i.e. not ~/.ssh/id_rsa and ~/.ssh/id_rsa.pub?
A: To use keys created with ssh-keygen in a different place than the default, perform these two tasks:
- The keys must be in a folder that only you can read or edit. If the folder has wider permissions, SSH will not use the keys.
- You must let SSH know the location of the keys. You make SSH aware of keys through the
ssh-addcommand, providing the full path to the private key.
On Windows, before running ssh-add, you will need to run the following command from included in Git for Windows:
This command runs in both PowerShell and the Command Prompt. If you are using Git Bash, the command you need to use is:
You can find ssh-add as part of the Git for Windows distribution and also run it in any shell environment on Windows.
On macOS and Linux you also must have ssh-agent running before running ssh-add, but the command environment on these platforms usuallytakes care of starting ssh-agent for you.
Q: I have multiple SSH keys. How do I use different SSH keys for different SSH servers or repos?
A: Generally, if you configure multiple keys for an SSH client and connect to an SSH server, the client can try the keys one at a time until the server accepts one.
However, this doesn't work with Azure DevOps for technical reasons related to the SSH protocol and how our Git SSH URLs are structured. Azure DevOps will blindly accept the first key that the client provides during authentication. If that key is invalid for the requested repo, the request will fail with the following error:
For Azure DevOps, you'll need to configure SSH to explicitly use a specific key file. One way to do this to edit your ~/.ssh/config file (for example, /home/jamal/.ssh or C:Usersjamal.ssh) as follows:
Q: How do I fix errors that mention 'no matching key exchange method found'?
A: Git for Windows 2.25.1 shipped with a new version of OpenSSH which removed some key exchange protocols by default.Specifically, diffie-hellman-group14-sha1 has been identified as problematic for some Azure DevOps Server and TFS customers.You can work around the problem by adding the following to your SSH configuration (~/.ssh/config):
Replace <your-azure-devops-host> with the hostname of your Azure DevOps or TFS server, like tfs.mycompany.com.
Q: What notifications may I receive about my SSH keys?
A: Whenever you register a new SSH Key with Azure DevOps Services, you will receive an email notification informing you that a new SSH key has been added to your account.
Q: What do I do if I believe that someone other than me is adding SSH keys on my account?
A: If you receive a notification of an SSH key being registered and you did not manually upload it to the service, your credentials may have been compromised.
The next step would be to investigate whether or not your password has been compromised. Changing your password is always a good first step to defend against this attack vector. If you’re an Azure Active Directory user, talk with your administrator to check if your account was used from an unknown source/location.
Q: What do I do if I'm still prompted for my password and GIT_SSH_COMMAND='ssh -v' git fetch shows no mutual signature algorithm?
A: Some Linux distributions, such as Fedora Linux, have crypto policies that require stronger SSH signature algorithms than Azure DevOps supports (as of January 2021). There's an open feature request to add this support.
You can work around the issue by adding the following code to your SSH configuration (~/.ssh/config):
Replace ssh.dev.azure.com with the correct host name if you use Azure DevOps Server.
предыдущая глава | содержание | следующая глава
Pre Generated Ssh Host Keys
This chapter lists a number of common error messages which PuTTY and its associated tools can produce, and explains what they mean in more detail.
We do not attempt to list all error messages here: there are many which should never occur, and some which should be self-explanatory. If you get an error message which is not listed in this chapter and which you don't understand, report it to us as a bug (see appendix B) and we will add documentation for it.
10.1 «The server's host key is not cached in the registry»
This error message occurs when PuTTY connects to a new SSH server. Every server identifies itself by means of a host key; once PuTTY knows the host key for a server, it will be able to detect if a malicious attacker redirects your connection to another machine.
If you see this message, it means that PuTTY has not seen this host key before, and has no way of knowing whether it is correct or not. You should attempt to verify the host key by other means, such as asking the machine's administrator.
If you see this message and you know that your installation of PuTTY has connected to the same server before, it may have been recently upgraded to SSH protocol version 2. SSH protocols 1 and 2 use separate host keys, so when you first use SSH-2 with a server you have only used SSH-1 with before, you will see this message again. You should verify the correctness of the key as before.
See section 2.2 for more information on host keys.
10.2 «WARNING - POTENTIAL SECURITY BREACH!»
This message, followed by «The server's host key does not match the one PuTTY has cached in the registry», means that PuTTY has connected to the SSH server before, knows what its host key should be, but has found a different one.
This may mean that a malicious attacker has replaced your server with a different one, or has redirected your network connection to their own machine. On the other hand, it may simply mean that the administrator of your server has accidentally changed the key while upgrading the SSH software; this shouldn't happen but it is unfortunately possible.
You should contact your server's administrator and see whether they expect the host key to have changed. If so, verify the new host key in the same way as you would if it was new.
See section 2.2 for more information on host keys.
10.3 «SSH protocol version 2 required by our configuration but remote only provides (old, insecure) SSH-1»
By default, PuTTY only supports connecting to SSH servers that implement SSH protocol version 2. If you see this message, the server you're trying to connect to only supports the older SSH-1 protocol.
If the server genuinely only supports SSH-1, then you need to either change the «SSH protocol version» setting (see section 4.19.4), or use the -1 command-line option; in any case, you should not treat the resulting connection as secure.
You might start seeing this message with new versions of PuTTY (from 0.68 onwards) where you didn't before, because it used to be possible to configure PuTTY to automatically fall back from SSH-2 to SSH-1. This is no longer supported, to prevent the possibility of a downgrade attack.
10.4 «The first cipher supported by the server is ... below the configured warning threshold»
This occurs when the SSH server does not offer any ciphers which you have configured PuTTY to consider strong enough. By default, PuTTY puts up this warning only for Blowfish, single-DES, and Arcfour encryption.
See section 4.22 for more information on this message.
(There are similar messages for other cryptographic primitives, such as host key algorithms.)
10.5 «Remote side sent disconnect message type 2 (protocol error): 'Too many authentication failures for root'»
This message is produced by an OpenSSH (or Sun SSH) server if it receives more failed authentication attempts than it is willing to tolerate.
This can easily happen if you are using Pageant and have a large number of keys loaded into it, since these servers count each offer of a public key as an authentication attempt. This can be worked around by specifying the key that's required for the authentication in the PuTTY configuration (see section 4.23.8); PuTTY will ignore any other keys Pageant may have, but will ask Pageant to do the authentication, so that you don't have to type your passphrase.
On the server, this can be worked around by disabling public-key authentication or (for Sun SSH only) by increasing MaxAuthTries in sshd_config.
10.6 «Out of memory»
This occurs when PuTTY tries to allocate more memory than the system can give it. This may happen for genuine reasons: if the computer really has run out of memory, or if you have configured an extremely large number of lines of scrollback in your terminal. PuTTY is not able to recover from running out of memory; it will terminate immediately after giving this error.
However, this error can also occur when memory is not running out at all, because PuTTY receives data in the wrong format. In SSH-2 and also in SFTP, the server sends the length of each message before the message itself; so PuTTY will receive the length, try to allocate space for the message, and then receive the rest of the message. If the length PuTTY receives is garbage, it will try to allocate a ridiculous amount of memory, and will terminate with an «Out of memory» error.
This can happen in SSH-2, if PuTTY and the server have not enabled encryption in the same way (see question A.7.3 in the FAQ).
This can also happen in PSCP or PSFTP, if your login scripts on the server generate output: the client program will be expecting an SFTP message starting with a length, and if it receives some text from your login scripts instead it will try to interpret them as a message length. See question A.7.4 for details of this.
10.7 «Internal error», «Internal fault», «Assertion failed»
Any error beginning with the word «Internal» should never occur. If it does, there is a bug in PuTTY by definition; please see appendix B and report it to us.
Similarly, any error message starting with «Assertion failed» is a bug in PuTTY. Please report it to us, and include the exact text from the error message box.
10.8 «Unable to use key file», «Couldn't load private key», «Couldn't load this key»
Various forms of this error are printed in the PuTTY window, or written to the PuTTY Event Log (see section 3.1.3.1) when trying public-key authentication, or given by Pageant when trying to load a private key.
If you see one of these messages, it often indicates that you've tried to load a key of an inappropriate type into PuTTY, Plink, PSCP, PSFTP, or Pageant.
You may have tried to load an SSH-2 key in a «foreign» format (OpenSSH or ssh.com) directly into one of the PuTTY tools, in which case you need to import it into PuTTY's native format (*.PPK) using PuTTYgen – see section 8.2.12.
Alternatively, you may have specified a key that's inappropriate for the connection you're making. The SSH-2 and the old SSH-1 protocols require different private key formats, and a SSH-1 key can't be used for a SSH-2 connection (or vice versa).
10.9 «Server refused our key», «Server refused our public key», «Key refused»
Various forms of this error are printed in the PuTTY window, or written to the PuTTY Event Log (see section 3.1.3.1) when trying public-key authentication.
If you see one of these messages, it means that PuTTY has sent a public key to the server and offered to authenticate with it, and the server has refused to accept authentication. This usually means that the server is not configured to accept this key to authenticate this user.
This is almost certainly not a problem with PuTTY. If you see this type of message, the first thing you should do is check your server configuration carefully. Common errors include having the wrong permissions or ownership set on the public key or the user's home directory on the server. Also, read the PuTTY Event Log; the server may have sent diagnostic messages explaining exactly what problem it had with your setup.
Section 8.3 has some hints on server-side public key setup.
10.10 «Access denied», «Authentication refused»
Various forms of this error are printed in the PuTTY window, or written to the PuTTY Event Log (see section 3.1.3.1) during authentication.
If you see one of these messages, it means that the server has refused all the forms of authentication PuTTY has tried and it has no further ideas.
Pre Generated Ssh Host Keys List
It may be worth checking the Event Log for diagnostic messages from the server giving more detail.
This error can be caused by buggy SSH-1 servers that fail to cope with the various strategies we use for camouflaging passwords in transit. Upgrade your server, or use the workarounds described in section 4.28.11 and possibly section 4.28.12.
10.11 «No supported authentication methods available»
This error indicates that PuTTY has run out of ways to authenticate you to an SSH server. This may be because PuTTY has TIS or keyboard-interactive authentication disabled, in which case see section 4.23.4 and section 4.23.5.
10.12 «Incorrect MAC received on packet» or «Incorrect CRC received on packet»
This error occurs when PuTTY decrypts an SSH packet and its checksum is not correct. This probably means something has gone wrong in the encryption or decryption process. It's difficult to tell from this error message whether the problem is in the client, in the server, or in between.
In particular, if the network is corrupting data at the TCP level, it may only be obvious with cryptographic protocols such as SSH, which explicitly check the integrity of the transferred data and complain loudly if the checks fail. Corruption of protocols without integrity protection (such as HTTP) will manifest in more subtle failures (such as misdisplayed text or images in a web browser) which may not be noticed.

Occasionally this has been caused by server bugs. An example is the bug described at section 4.28.8, although you're very unlikely to encounter that one these days.
In this context MAC stands for Message Authentication Code. It's a cryptographic term, and it has nothing at all to do with Ethernet MAC (Media Access Control) addresses, or with the Apple computer.
10.13 «Incoming packet was garbled on decryption»
This error occurs when PuTTY decrypts an SSH packet and the decrypted data makes no sense. This probably means something has gone wrong in the encryption or decryption process. It's difficult to tell from this error message whether the problem is in the client, in the server, or in between.
If you get this error, one thing you could try would be to fiddle with the setting of «Miscomputes SSH-2 encryption keys» (see section 4.28.10) or «Ignores SSH-2 maximum packet size» (see section 4.28.5) on the Bugs panel.
10.14 «PuTTY X11 proxy: various errors»
This family of errors are reported when PuTTY is doing X forwarding. They are sent back to the X application running on the SSH server, which will usually report the error to the user.
When PuTTY enables X forwarding (see section 3.4) it creates a virtual X display running on the SSH server. This display requires authentication to connect to it (this is how PuTTY prevents other users on your server machine from connecting through the PuTTY proxy to your real X display). PuTTY also sends the server the details it needs to enable clients to connect, and the server should put this mechanism in place automatically, so your X applications should just work.
A common reason why people see one of these messages is because they used SSH to log in as one user (let's say «fred»), and then used the Unix su command to become another user (typically «root»). The original user, «fred», has access to the X authentication data provided by the SSH server, and can run X applications which are forwarded over the SSH connection. However, the second user («root») does not automatically have the authentication data passed on to it, so attempting to run an X application as that user often fails with this error.
If this happens, it is not a problem with PuTTY. You need to arrange for your X authentication data to be passed from the user you logged in as to the user you used su to become. How you do this depends on your particular system; in fact many modern versions of su do it automatically.
10.15 «Network error: Software caused connection abort»
This is a generic error produced by the Windows network code when it kills an established connection for some reason. For example, it might happen if you pull the network cable out of the back of an Ethernet-connected computer, or if Windows has any other similar reason to believe the entire network has become unreachable.
Windows also generates this error if it has given up on the machine at the other end of the connection ever responding to it. If the network between your client and server goes down and your client then tries to send some data, Windows will make several attempts to send the data and will then give up and kill the connection. In particular, this can occur even if you didn't type anything, if you are using SSH-2 and PuTTY attempts a key re-exchange. (See section 4.20.2 for more about key re-exchange.)
(It can also occur if you are using keepalives in your connection. Other people have reported that keepalives fix this error for them. See section 4.14.1 for a discussion of the pros and cons of keepalives.)
We are not aware of any reason why this error might occur that would represent a bug in PuTTY. The problem is between you, your Windows system, your network and the remote system.
10.16 «Network error: Connection reset by peer»
This error occurs when the machines at each end of a network connection lose track of the state of the connection between them. For example, you might see it if your SSH server crashes, and manages to reboot fully before you next attempt to send data to it.
However, the most common reason to see this message is if you are connecting through a firewall or a NAT router which has timed the connection out. See question A.7.8 in the FAQ for more details. You may be able to improve the situation by using keepalives; see section 4.14.1 for details on this.
Note that Windows can produce this error in some circumstances without seeing a connection reset from the server, for instance if the connection to the network is lost.
10.17 «Network error: Connection refused»
This error means that the network connection PuTTY tried to make to your server was rejected by the server. Usually this happens because the server does not provide the service which PuTTY is trying to access.
Check that you are connecting with the correct protocol (SSH, Telnet or Rlogin), and check that the port number is correct. If that fails, consult the administrator of your server.
10.18 «Network error: Connection timed out»
This error means that the network connection PuTTY tried to make to your server received no response at all from the server. Usually this happens because the server machine is completely isolated from the network, or because it is turned off.
Check that you have correctly entered the host name or IP address of your server machine. If that fails, consult the administrator of your server.
Unix also generates this error when it tries to send data down a connection and contact with the server has been completely lost during a connection. (There is a delay of minutes before Unix gives up on receiving a reply from the server.) This can occur if you type things into PuTTY while the network is down, but it can also occur if PuTTY decides of its own accord to send data: due to a repeat key exchange in SSH-2 (see section 4.20.2) or due to keepalives (section 4.14.1).
10.19 «Network error: Cannot assign requested address»
This means that the operating system rejected the parameters of the network connection PuTTY tried to make, usually without actually trying to connect to anything, because they were simply invalid.
A common way to provoke this error is to accidentally try to connect to port 0, which is not a valid port number.
Pre Generated Ssh Host Keys Free
При использовании материалов сайта указывайте источник.